- Indico style
- Indico style - inline minutes
- Indico style - numbered
- Indico style - numbered + minutes
- Indico Weeks View
OARC 26 (Madrid)
→
Europe/Madrid
,
Description
DNS-OARC is traveling to Madrid, Spain for its 26th Workshop!
DNS-OARC is a non-profit, membership organization that seeks to improve the security, stability, and understanding of the Internet's DNS infrastructure. Part of these aims are achieved through workshops.
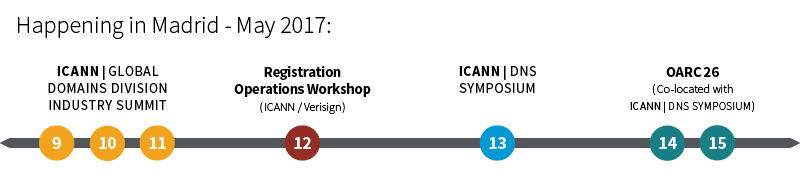
The workshops are open to OARC members and to all other parties interested in DNS operations and research, with attendees from ICANN GDD Industry Summit 2017, the 6th Registration Operations Workshop, and the ICANN DNS Symposium particularly welcome this time around - as OARC 26 takes place just after these in the same venue in Madrid. Attendance is free for OARC Members, Speakers and Sponsors. There are charges for other attendees and late registrations.
We are thankful to our Host and sponsors for supporting OARC 26.
HOST
PREMIUM SPONSOR
PATRON SPONSOR
Webcast Video
Jabber: dns-operations@conference.dns-oarc.net
Twitter hashtag: #OARC26
Sponsors: We have various sponsor opportunities for OARC 26, and OARC 27.
If your organization is interested in sponsoring OARC workshops, please see our Sponsor Benefits or e-mail sponsor@dns-oarc.net for more information.
Support - Help
Participants
Adiel Akplogan (ICANN)
Adrian Beaudin
Alexander Mayrhofer
Alexandra Kulikova
Amanda Swain
Andrew White
Angelo Conforti
Anton Holleman
Arjen Zonneveld
Arnaud JOLIVET
Benedict Addis
Benjamin Zwittnig
Bert Hubert
Bjorn Hellqvist
Boban Krsic
Brad Verd
Brett Carr
Carl Clements
Cathy Almond
Cathy Petersen
Chris Cowherd
Christian Petrasch
Christian Simmen
Daniel Griggs
Daniel Stirnimann
Danillo Roncoleta
Dave Knight
David Conrad
David Lawrence
Denesh Bhabuta
Dmitry Kohmanyuk
Domagoj Klemen Markovic
Dominic Marks
Dong XU
Duane Wessels
Eddy Winstead
Eduardo Alvarez
Eduardo Duarte
Eduardo Mercader
Eduardo Pszczol
Edward Lewis
Enrique Gonzalez
Erwin Lansing
Evan Thompson
Felipe Agnelli
Florian Obser
Francisco Arias
Gavin Brown
Geoff Horne
Geoff Huston
Georg Kahest
George Sadowsky
Geriet Wendler
Giovane Moura
Greg Choules
Gustavo Lozano
Ivan Capan
Iñigo Ortiz de Urbina Cazenave
Jacob Zack
Jacques Latour
Jaeson Schultz
Jan Včelák
Jaromir Talir
Jeff Osborn
Jeff Schmidt
Jerry Lundström
Jesse Sowell
Jim Reid
Joao Luis Silva Damas
Johan Ihrén
John Crain
John Dickinson
John Todd
Jorge Cano Puente
João Matheus Ampessan Schiavo
Juan P. Cerezo
Jurong Li
Karl Dyson
Karl Reuss
Kaveh Ranjbar
Keith Mitchell
Kim Davies
Konstantin Novakovskii
Leo van de Woestijne
Liam Hynes
Linjian Song
Maarten Wullink
Maciej Korczynski
Manu Bretelle
Marc Whittaker
Marcelo Guimarães de Oliveira
Marco Diaz
Marco Pizzoli
Mark Gaudet
Matt Larson
Matt Weinberg
Matthew Pounsett
Maurice van der Meer
Mauricio Vergara Ereche
Melanie Cruz
Merike Kaeo
Mikael Kullberg
Mike Brennan
Mirko Mirkovic
Mohammed Zakir Patel
Negar Farzinnia
Nico CARTRON
Normen Kowalewski
Oleg Levchenko
Oli Schacher
Ondrej Sury
Patrick Jones
Paul Ebersman
Paul Hoffman
Pavel Odintsov
Peter Hagopian
peter Janssen
Peter Koch
Peter Popovich
Peter van Dijk
Petr Andreev
Petr Špaček
Piet Barber
Pieter Lexis
Ralf Weber
Ralph Dolmans
Ray Bellis
Richard Lamb
Rinalia Abdul Rahim
Robert Edmonds
Roger Murray
Rogerio Cunha
Roland van Rijswijk-Deij
Roy Arends
Roy Hooper
Rubens Kuhl
Santiago Ruano Rincón
Sara Dickinson
Shane Kerr
Shumon Huque
Stephen Morris
Steve Crocker
Sue Graves
Tom Arnfeld
Tongfeng Zhang
Ulrich Wisser
Victoria Risk
Vincent CHARRADE
Vincent Levigneron
Vladimir Aleksic
Willem Toorop
Yuedong Zhang
Yves Bovard
Ólafur Guðmundsson

